The battlefield of the 21st century exists not in trenches or airspace, but in fiber optic cables, data centers, and electromagnetic spectrum. As nations increasingly depend on digital infrastructure for everything from banking to healthcare, the ability to control, protect, and leverage cyberspace has become synonymous with sovereignty itself. This new reality is forcing governments to reimagine national defense, citizenship rights, and the very concept of territorial integrity in an age where borders dissolve into packets of data traveling at light speed.
The Architecture of Digital Sovereignty
Digital sovereignty encompasses a nation’s ability to control its information space, protect citizen data, and maintain independence in critical digital infrastructure. Unlike traditional sovereignty based on physical territory, cyber sovereignty operates across multiple layers: the physical infrastructure of cables and servers, the logical layer of protocols and software, and the content layer of information and services.
The Physical Layer: Infrastructure as Power
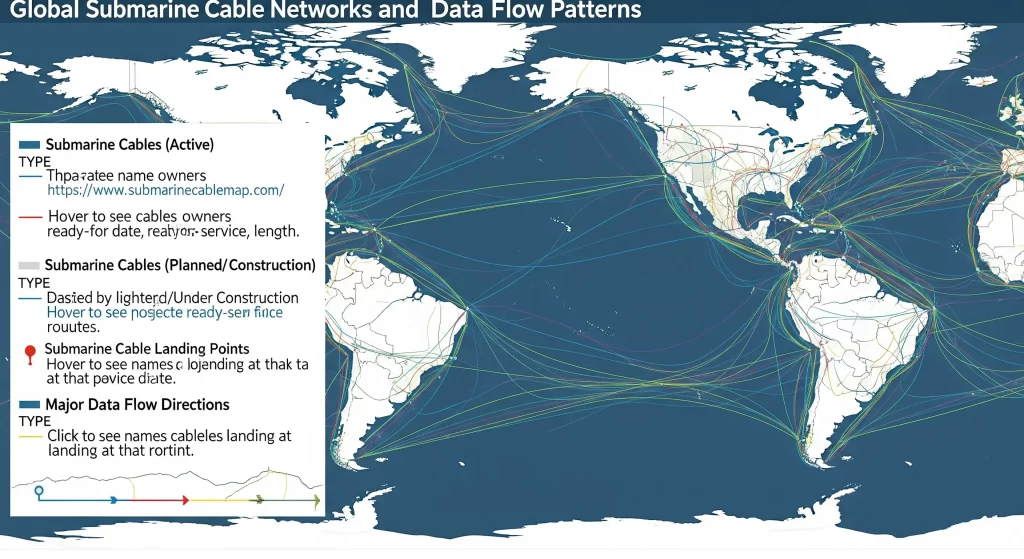
Undersea cables carry 99% of international data traffic, making their control a strategic imperative. The approximately 550 submarine cables worldwide represent chokepoints more critical than oil shipping lanes. Nations controlling cable landing points possess the ability to monitor, throttle, or sever global communications.
China’s Digital Silk Road has invested $79 billion in digital infrastructure across 100 countries, including cables, data centers, and smart cities. The PEACE cable, connecting Pakistan, East Africa, and Europe, bypasses traditional routes through Egypt and the Suez Canal, creating alternative pathways under Chinese influence. This infrastructure investment grants Beijing unprecedented access to global data flows.
The United States, through companies like Google, Microsoft, and Amazon, controls approximately 60% of global cloud infrastructure. This dominance means that most international data, even between two non-American entities, likely passes through US-controlled servers, granting potential access to intelligence agencies under laws like the CLOUD Act.
The Logical Layer: Protocols and Standards
Control over internet protocols and standards represents invisible but immense power. The Internet Corporation for Assigned Names and Numbers (ICANN), historically under US influence, manages critical internet resources like domain names and IP addresses. This control theoretically allows cutting entire nations from the global internet.
China and Russia have promoted alternative internet governance through the International Telecommunication Union (ITU), a UN agency. Their “New IP” proposal would embed government control into internet architecture, enabling automatic censorship and surveillance at the protocol level. While Western nations have resisted, the proposal’s support from developing nations signals growing desire for alternatives to US-dominated systems.
5G standards have become a sovereignty battlefield. Huawei’s 5G patents and equipment dominance initially positioned China to shape global communications infrastructure. The subsequent US-led campaign against Huawei, citing security concerns, demonstrates how technical standards intertwine with geopolitical competition.
The Great Fragmentation: From One Internet to Many
China’s Sovereign Internet Model
China’s approach to cyber sovereignty represents the most comprehensive attempt to create a parallel digital ecosystem. The Great Firewall, officially the Golden Shield Project, employs deep packet inspection, keyword filtering, and IP blocking to control information flow. Beyond mere censorship, it has fostered domestic alternatives to global platforms: Baidu replacing Google, WeChat substituting WhatsApp, and Alibaba competing with Amazon.
The 2017 Cybersecurity Law mandates data localization, requiring companies to store Chinese citizens’ data within China. Foreign companies must partner with local entities and submit to security reviews, effectively granting the government access to any data within its borders. This model has proven so effective that other nations increasingly adopt similar measures.
China’s social credit system demonstrates cyber sovereignty’s domestic dimensions. By integrating government databases with private platforms, the system creates unprecedented surveillance and control capabilities. Citizens’ digital activities directly impact real-world opportunities, from travel rights to employment prospects, merging digital and physical sovereignty.
Russia’s Sovereign Internet Law
Russia’s 2019 Sovereign Internet Law creates infrastructure for disconnecting from the global internet while maintaining domestic connectivity. The law requires ISPs to install deep packet inspection equipment, creating a single point of control for Russian internet traffic. Annual disconnection tests verify the system’s effectiveness.
The Yarovaya Laws require telecommunications companies to store all communications metadata for three years and content for six months, accessible to security services without court orders. Combined with requirements for messaging apps to provide encryption keys, these laws establish comprehensive surveillance capabilities.
Russia has developed domestic alternatives to critical internet services: Yandex for search, VKontakte for social networking, and Mir payment system replacing Visa and Mastercard. These platforms reduce dependency on Western services while providing government-accessible data repositories.
The European Union’s Digital Sovereignty
The EU’s approach emphasizes regulatory sovereignty rather than technical isolation. The General Data Protection Regulation (GDPR) asserts jurisdiction over any company processing EU citizens’ data, regardless of location. With fines reaching 4% of global revenue, GDPR has forced worldwide companies to adapt to European standards.
The Digital Services Act and Digital Markets Act further extend EU regulatory reach, mandating content moderation standards and limiting big tech monopolistic practices. The proposed Data Act would require cloud providers to enable data portability, preventing vendor lock-in and ensuring European data sovereignty.
Project GAIA-X aims to create a federated European cloud infrastructure, reducing dependence on American and Chinese providers. While progress remains slow, the initiative represents Europe’s recognition that digital sovereignty requires indigenous technical capabilities, not just regulations.

Cyber Warfare: The Fifth Domain of Conflict
State-Sponsored Cyber Operations
Nation-state cyber operations have evolved from espionage tools to weapons of war. The 2007 cyberattacks on Estonia, attributed to Russia, paralyzed government services, banks, and media outlets, demonstrating cyber weapons’ potential to cripple nations without firing a shot. The 2010 Stuxnet attack on Iranian nuclear facilities, allegedly by the US and Israel, proved that cyberweapons could cause physical destruction.
Advanced Persistent Threats (APTs) represent long-term intrusions by state actors. China’s APT1 unit has allegedly stolen hundreds of terabytes of intellectual property from Western companies. Russia’s Fancy Bear group has interfered in elections across Europe and America. These operations blur lines between espionage, sabotage, and warfare.
The NotPetya malware, initially targeting Ukraine, caused $10 billion in global damages, affecting companies from Maersk shipping to Merck pharmaceuticals. This incident demonstrated how cyberweapons can escape control, causing collateral damage far beyond intended targets. The attribution challenges and lack of international norms make cyber operations attractive options for state aggression.
Critical Infrastructure Vulnerabilities
Power grids, water systems, and transportation networks increasingly depend on internet-connected systems. The 2021 Colonial Pipeline ransomware attack disrupted fuel supplies across the US Eastern Seaboard, demonstrating critical infrastructure vulnerability. The attack, by criminal group DarkSide, showed how non-state actors could achieve strategic effects previously reserved for nation-states.
Healthcare systems represent particularly vulnerable targets. The 2017 WannaCry ransomware affected Britain’s National Health Service, forcing hospitals to cancel surgeries and redirect emergency patients. During COVID-19, cyberattacks on hospitals and vaccine researchers highlighted healthcare infrastructure as a national security concern.
Financial systems face constant assault. The 2016 Bangladesh Bank heist, where hackers stole $81 million through the SWIFT network, revealed vulnerabilities in global financial infrastructure. Central Bank Digital Currencies (CBDCs) are partly motivated by desires to create more controllable, defensible monetary systems.
The Attribution Problem
Cyberattacks’ anonymous nature creates an attribution problem that undermines traditional deterrence. Attackers route operations through multiple countries, use compromised systems as proxies, and employ false flags to misdirect blame. This ambiguity enables plausible deniability and complicates responses.
The “Defend Forward” doctrine adopted by US Cyber Command represents one response, conducting offensive operations to disrupt adversaries before attacks materialize. However, this approach risks escalation and normalizes cyberattacks as acceptable state behavior. The lack of agreed norms analogous to Geneva Conventions for cyberspace creates a digital Wild West.

Digital Citizenship: Rights and Surveillance in the Connected Age
The Surveillance State Evolution
Edward Snowden’s 2013 revelations exposed the extent of digital surveillance capabilities, showing how intelligence agencies collect, store, and analyze vast quantities of citizen communications. Programs like PRISM and XKeyscore demonstrated that digital surveillance had already exceeded Orwellian imagination.
China’s Sharp Eyes program aims to surveil every citizen through 600 million cameras equipped with facial recognition. The system can identify individuals in crowds, track movements across cities, and alert authorities to “abnormal” behavior. Combined with smartphone tracking and digital payment monitoring, it creates comprehensive surveillance unprecedented in human history.
Pegasus spyware, sold by Israeli company NSO Group, has been used by governments worldwide to surveil journalists, activists, and political opponents. The software’s ability to access encrypted communications, activate cameras and microphones, and extract all device data has turned smartphones into perfect surveillance devices.
Digital Rights as Human Rights
The UN Human Rights Council declared internet access a human right in 2016, recognizing digital participation as essential for modern life. However, internet shutdowns have become common government tools for controlling dissent. In 2023, governments imposed 283 internet shutdowns across 39 countries, affecting billions of people.
Encryption represents a fundamental battleground between privacy and security. Governments argue that end-to-end encryption protects criminals and terrorists, demanding “backdoors” for law enforcement. Privacy advocates counter that weakening encryption compromises everyone’s security, creating vulnerabilities that criminals and foreign adversaries will exploit.
The right to be forgotten, established in EU law, allows individuals to request removal of personal information from search engines. This concept challenges American free speech principles and global internet architecture. The conflict between privacy rights and information freedom highlights fundamental disagreements about digital citizenship.
Biometric Identity Systems
India’s Aadhaar system, covering 1.3 billion people, represents the world’s largest biometric identity program. The system links fingerprints and iris scans to a unique number required for government services, banking, and phone connections. While improving service delivery and reducing fraud, it creates surveillance capabilities and exclusion risks for those unable or unwilling to enroll.
Digital identity systems are proliferating globally. Estonia’s e-Residency program allows anyone worldwide to establish a digital identity and access Estonian services. China’s blockchain-based identity system aims to create tamper-proof digital identities. These systems promise efficiency but concentrate enormous power over citizens’ ability to participate in society.

The Data Economy: Information as the New Oil
Data Localization and Economic Sovereignty
Data localization laws, requiring data storage within national borders, have proliferated from 35 countries in 2015 to over 140 in 2024. These laws aim to ensure government access for law enforcement, protect citizen privacy from foreign surveillance, and develop domestic tech industries. However, they fragment the global internet and increase costs for international businesses.
Russia’s data localization requirements have forced companies like LinkedIn to exit the market rather than comply. India’s proposed Data Protection Bill would require copies of all personal data to remain in India, affecting global tech giants’ operations. These requirements create technical challenges and legal conflicts for multinational companies operating across jurisdictions.
The economic impact extends beyond compliance costs. Data localization can foster domestic tech industries by creating competitive advantages for local companies. It also ensures that the economic value generated from citizen data remains within national economies rather than flowing to foreign tech giants.
Platform Power and Digital Colonialism
American tech platforms—Google, Amazon, Facebook, Apple, Microsoft—dominate global digital infrastructure. Their services have become essential utilities, yet operate beyond traditional government oversight. This dominance has led to accusations of “digital colonialism,” where developing nations depend on foreign platforms that extract data and economic value.
China’s digital platforms—Alibaba, Tencent, ByteDance—offer alternatives but raise similar sovereignty concerns. TikTok’s success in Western markets triggered national security reviews, with several countries banning or restricting the app over data collection concerns. The forced sale discussions demonstrate how platform control intersects with national security.
The platform economy’s network effects create winner-take-all dynamics that challenge traditional competition law. The EU’s Digital Markets Act attempts to address this by designating certain platforms as “gatekeepers” subject to additional obligations. However, regulating global platforms requires international coordination that current governance structures struggle to provide.
Cryptocurrency and Monetary Sovereignty
Cryptocurrencies challenge state monopolies over money creation and financial surveillance. Bitcoin’s pseudonymous transactions enable cross-border transfers outside government control, threatening capital controls and tax collection. This has prompted responses ranging from outright bans to attempts at co-option.
Central Bank Digital Currencies (CBDCs) represent states’ attempts to maintain monetary sovereignty while capturing digital currency benefits. China’s digital yuan, already in limited circulation, provides transaction efficiency while maintaining government oversight. The currency’s programmability enables unprecedented monetary control, including expiration dates and spending restrictions.
The dollar’s dominance in international finance has long provided the United States with “exorbitant privilege.” As countries develop alternative payment systems and digital currencies, this financial sovereignty tool may weaken. Russia and China’s efforts to create SWIFT alternatives and promote non-dollar trade reflect desires to escape US financial surveillance and sanctions.

Technological Dependencies and Supply Chain Sovereignty
The Semiconductor Chokepoint
Semiconductors represent perhaps the most critical technological dependency. Taiwan produces 92% of advanced chips, while ASML in the Netherlands holds monopoly over extreme ultraviolet lithography machines essential for chip production. This concentration creates existential vulnerabilities for nations dependent on digital technologies.
The US CHIPS Act allocates $52 billion to rebuild domestic semiconductor manufacturing, recognizing that chip dependence threatens economic and military security. China invests $150 billion in semiconductor self-sufficiency, though technical challenges mean independence remains years away. The EU aims for 20% of global chip production by 2030.
Export controls on semiconductor technology have become weapons in tech competition. US restrictions on selling advanced chips and manufacturing equipment to China aim to maintain technological advantage. These controls force other nations to choose sides, fragmenting global supply chains.
Software Dependencies and Open Source
Most critical infrastructure runs on software with foreign dependencies. Microsoft Windows operates on most government computers worldwide. Oracle databases store sensitive government data. These dependencies create vulnerabilities that adversaries can exploit.
Open-source software offers potential sovereignty through transparency and community control. However, even open-source projects often depend on small numbers of volunteer maintainers, creating different vulnerabilities. The 2021 Log4j vulnerability, affecting countless systems worldwide, demonstrated how obscure software components can create systemic risks.
Nations increasingly mandate source code reviews and security audits for critical systems. Russia’s law requiring foreign software companies to provide source code for security products operating in government systems exemplifies this trend. While improving security, such requirements also enable intellectual property theft and create market barriers.
Future Scenarios: The Shape of Digital Sovereignty
The Splinternet Scenario
The most likely future involves continued internet fragmentation along geopolitical lines. Regional internets with limited interconnection would replace today’s global network. Digital borders would mirror physical ones, with data “passports” required for cross-border information flow.
This scenario sees tech stacks aligned with geopolitical blocs: Western systems built on US platforms, Eurasian systems on Chinese/Russian alternatives, and the EU potentially developing indigenous capabilities. Developing nations would face pressure to choose sides, limiting their digital sovereignty.
The splinternet would reduce innovation through decreased collaboration and market fragmentation. However, it might also foster diversity in digital development models and reduce systemic vulnerabilities from shared dependencies.
The Corporate Sovereignty Scenario
Alternatively, tech corporations might eclipse nation-states in cyberspace control. With resources exceeding many national budgets and technical capabilities surpassing government understanding, tech giants could become de facto sovereign entities in digital space.
This scenario envisions corporate-issued digital identities, private digital currencies, and platform-based governance systems. Nations would negotiate with tech companies as equals rather than regulate them as subjects. Digital citizenship would depend more on platform membership than national identity.
Meta’s attempted Libra currency and Amazon’s company towns suggest corporate sovereignty aspirations. While nations have thus far resisted, continued government technical incompetence and corporate innovation could shift the balance.
The Quantum Revolution Scenario
Quantum computing could render current encryption obsolete, fundamentally disrupting digital sovereignty. The nation first achieving quantum supremacy would possess the ability to decrypt any communication, access any system, and compromise any digital security.
This scenario requires massive investment in quantum-safe cryptography and new security architectures. The quantum race parallels nuclear weapon development in its potential to create decisive strategic advantage. Unlike nuclear weapons, however, quantum computing’s dual-use nature makes control regimes difficult.
Post-quantum cryptography development represents a critical sovereignty requirement. Nations unable to transition before adversaries achieve quantum capabilities would lose digital sovereignty entirely.
Conclusion: Sovereignty Reimagined for the Digital Age
The concept of sovereignty, unchanged since the 1648 Peace of Westphalia, requires fundamental reimagining for the digital age. Cyberspace’s borderless nature, the speed of digital attacks, and data’s economic value challenge traditional notions of territorial integrity and national defense. Nations must simultaneously protect physical infrastructure, logical protocols, and information flows while balancing security with innovation and control with openness.
The struggle for cyber sovereignty reflects deeper questions about power in the 21st century. Can democratic values survive in surveilled digital spaces? Will technological dependencies create new forms of colonialism? How can nations protect citizens without destroying the internet’s innovative capacity? These questions lack easy answers, but their resolution will shape humanity’s digital future.
Success in establishing cyber sovereignty requires more than technical capabilities. It demands new international norms, innovative governance models, and careful balance between competing values. Nations must invest in digital infrastructure, develop indigenous capabilities, and educate citizens for digital participation while avoiding the trap of digital authoritarianism.
The battle for sovereignty in bits represents more than technological competition; it’s a struggle for the future of human organization in an interconnected world. As physical and digital worlds merge, the distinction between cyber and traditional sovereignty dissolves. The nations that successfully navigate this transformation will define the 21st century’s global order.
Digital sovereignty isn’t about building walls in cyberspace but about maintaining agency in an interconnected world. It requires the wisdom to know what to protect, the capability to protect it, and the restraint to avoid destroying the digital commons in the name of security. The choices made today about internet governance, data protection, and digital rights will reverberate for generations.
The ultimate question isn’t whether nations can achieve absolute cyber sovereignty—they cannot. Instead, it’s how to maintain sufficient digital autonomy while participating in global digital society. This balance, different for each nation based on its values, capabilities, and circumstances, will determine winners and losers in the new digital great game.